Typical CMMC L1 consultant
~$50,000
One-time readiness engagement. Hand-held through prep, then handed back to you with a workbook to maintain on your own.
For SMB DoD subcontractors
Write your implementation narratives, attach evidence, walk an annual cycle, and generate the SPRS submission package — in software, not in Excel. Affirmark covers the 15 L1 requirements and 59 assessment objectives, monitors them continuously between cycles, and gives your assessor a verifiable audit chain to check offline. Same platform when you step up to Level 2.
See pricing →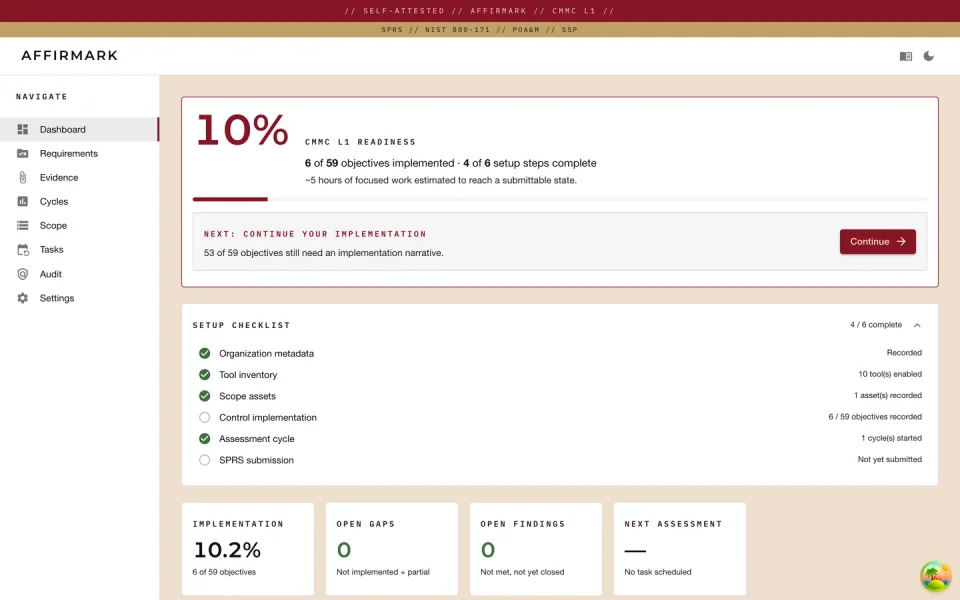
Pricing
$399 per month per organization. Continuous workflow, annual cycle, SPRS submission package, verifiable audit chain — yours every year, not a one-time engagement. A typical CMMC L1 readiness consultant runs ~$50,000.
Typical CMMC L1 consultant
~$50,000
One-time readiness engagement. Hand-held through prep, then handed back to you with a workbook to maintain on your own.
Affirmark
$399 / month
Per organization, unlimited seats. Deployed in your AWS, Azure, GCP, or on-prem environment — your data, your boundary. Annual cycle, SPRS submission package, and an assessor-defensible audit chain — every year, not just at first prep.
Platform license Versioned Terraform module + container images, deployed in your environment.
Continuous control monitoring Mailbox + API ingestion from your IdP, EDR, and scanner stack — drift surfaces in near real time, not at the next cycle close.
Framework updates When DoD revises CMMC L1, Affirmark ships a release reflecting it; your narratives, evidence, and audit chain carry forward.
Security patches Critical fixes flagged in release notes, deployment owner notified directly.
Email support 72-hour SLA on non-critical issues, 24-hour on critical.
One organization. Unlimited seats. Hosted in your environment — AWS, Azure, GCP, or on-prem. No setup fee. Cancel any time.
See what's included →Design-partner cohort
Now open to a small set of SMB DoD subcontractors. We work with each one through their first SPRS cycle before broader release.
I · The Problem
DoD contracts include FAR 52.204-21 — basic safeguarding for Federal Contract Information — and almost all of them require it. CMMC 2.0 (32 CFR Part 170) makes the L1 attestation enforceable: by Phase 3 in December 2026, no DoD contract is awarded without a current SPRS score from the contractor and every subcontractor in scope. If your prime just asked for yours, this is for you.
Handling FCI
CMMC Level 1 — self-attested annually in SPRS. Affirmark covers this end-to-end.
Handling CUI
CMMC Level 2 — third-party assessed by a C3PAO every three years. Affirmark's same database scales to L2.
FAR 52.204-21 mandates 15 basic safeguarding requirements for any contractor or subcontractor handling Federal Contract Information. Every requirement applies to your business — there is no L1 partial scope.
The CMMC Level 1 Assessment Guide decomposes those 15 requirements into 59 testable objectives. Each one needs an implementation narrative, evidence, and a finding of met or not applicable — nothing left open when you submit.
Once a year, a senior official at your company has to sign an affirmation and submit it to the Supplier Performance Risk System. They affirm under penalty that all 59 objectives are continuously satisfied. The clock starts the day you ship.
The stakes
Missing the deadline can suspend contract performance and cost you future awards. A knowingly false attestation triggers False Claims Act exposure — civil penalties run roughly $14K-$28K per false claim, plus treble damages. The DOJ has settled cybersecurity-attestation FCA cases against contractors for over $9M.
II · Approach
The 16-sheet workbook a CMMC consultant leaves with you is a deliverable, not a tool. Affirmark makes the database the source of truth and generates the workbook on demand when an assessor asks.
Capture your stack once at setup — IdP, EDR, MDM, backup, cloud — and Affirmark narrows the responsible-tool dropdowns and pre-populates defaults across all 59 objectives. Verbatim CMMC text on the left, your narrative editor on the right, sized for the tool you actually use.
Upload screenshots, configuration exports, attestation letters, scan reports — or, for several Tier-A providers, let Affirmark pull from your IdP, EDR, and scanner inboxes directly. Every artifact is hashed and can support multiple objectives; a freshness clock tracks expiry; you mark which artifact is doing the heavy lifting so the assessor reads what matters first.
Walk every objective via examine, interview, or test; closing is blocked while any finding is still open. Once the cycle closes clean, Affirmark composes the SPRS submission package — metadata, scope, 59 findings, affirmation template — ready for your senior official to sign.
Every write to a compliance entity appends an entry to a hash-chained log; a single command walks the chain end-to-end. Each closed cycle snapshots the chain head, so an assessor can verify nothing has been altered after the fact.
Affirmark does not submit to SPRS for you. The portal is human-driven by regulatory design — the senior official signs the affirmation in SPRS personally. We produce every artifact the portal asks for, ready for the moment they sign.
III · AI Intake
Affirmark's AI Intake is the fastest path from "we just inherited the CMMC requirement" to an SPRS-ready baseline. Pick the tools you actually use, answer six strategic questions, and Claude drafts proposed implementations for all 59 L1 objectives in ~60 seconds — grounded in your stack, not generic boilerplate.
Grounded
The intake reads the tools you've enabled in inventory — Entra ID, Defender, Tenable,
Tailscale — and grounds every narrative in those product names. No [TOOL] placeholders to fill in by hand later.
Reviewable
The 59 drafts land on a review screen — accept individually, edit inline, or regenerate the batch. Every accepted row is flagged AI-assisted with the model id captured, so the assessor sees exactly what the LLM produced versus what your team confirmed.
Auditable
Each accepted row writes to the same hash-chained audit log every other compliance entity touches. Your senior official signs an SPRS package built from drafts you reviewed, stamped with the model that proposed them, anchored to a verifiable chain.
Or skip ahead — see all six product surfaces below.
Now shipping
Affirmark monitors your tooling — IdP, EDR, vulnerability scanners, configuration sources — and pulls fresh evidence the moment a control changes. Mailbox-driven (Microsoft 365, Google Workspace, Proton) or direct API. Drift surfaces in near real time; your audit chain stays current between cycles; annual affirmation becomes a refresh, not a redo. Supported for several Tier-A providers today, with more wiring in continuously.
Evidence flows in as your tooling reports it — no end-of-year scramble.
Control changes surface in the moment, not at the next cycle close.
Annual affirmations become a re-confirm, not a re-do.
IV · See it
Synthetic data — Apex Logistics, LLC, fictional NAICS 488510 freight subcontractor — but every interaction shown is the real product.
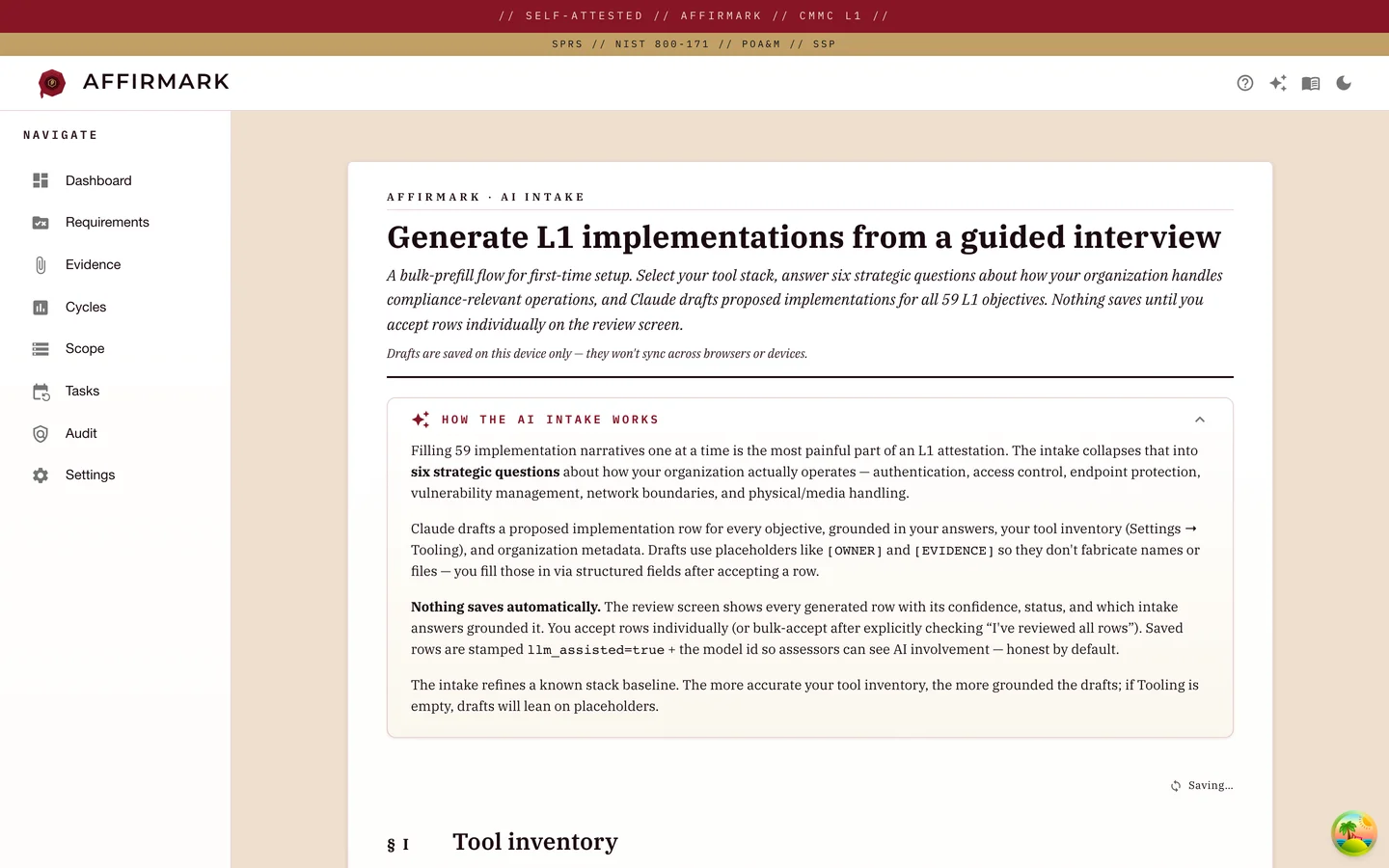
AI Intake
Pick the tools you actually use. Answer six strategic questions about authentication, access control, endpoints, vulnerability management, network boundaries, and physical media. Claude streams 59 grounded control-implementation drafts in real time. Nothing saves until you accept rows on the review screen — the assessor sees AI-assisted drafts you confirmed, not generic boilerplate.
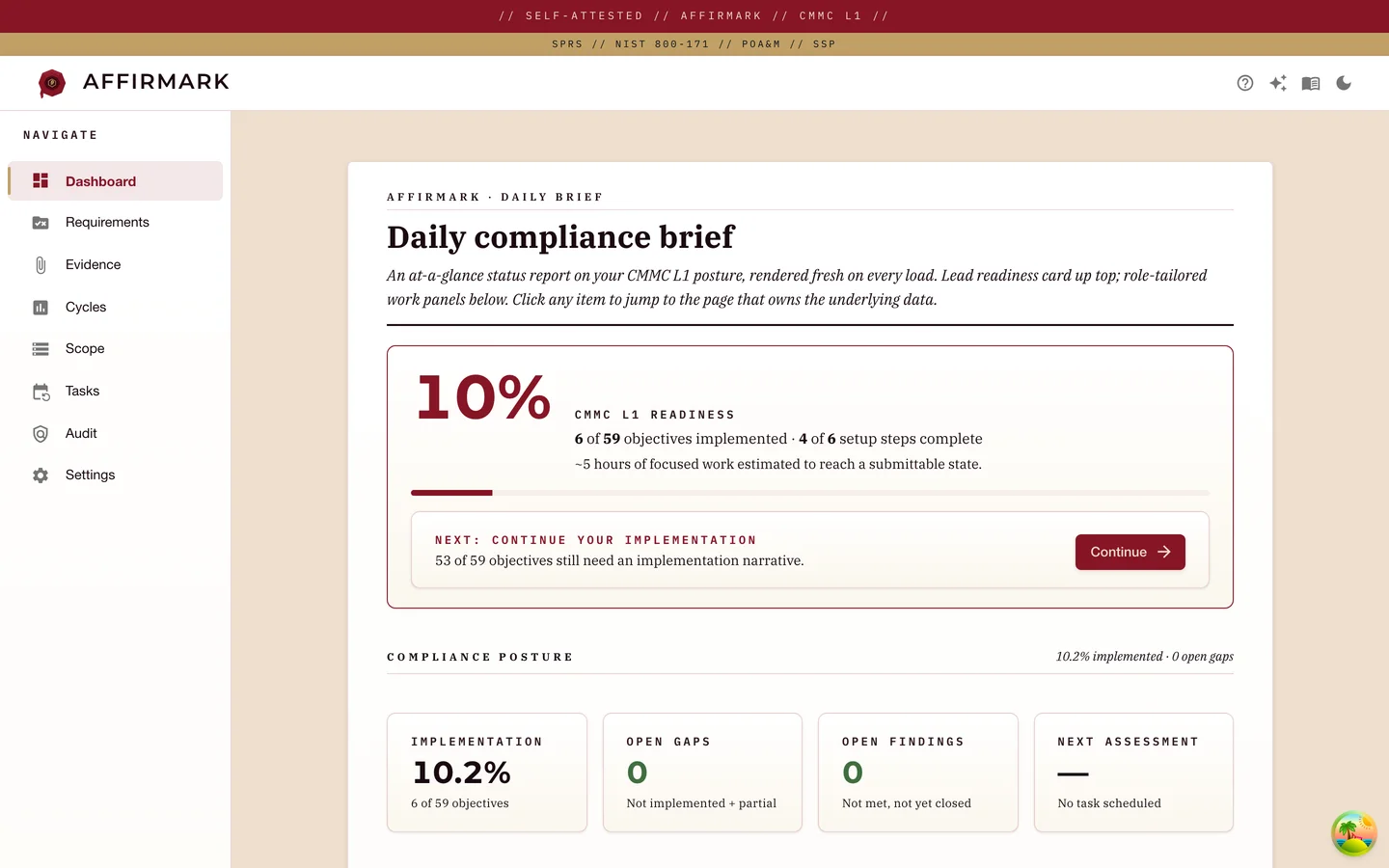
Dashboard
L1 readiness percentage, the next-best-action prompt, the setup checklist, and the four numbers your senior official asks about — implementation, open gaps, open findings, next assessment. The first screen your L1 manager checks at the start of the day.
![Affirmark objective-detail screen for AC.L1-b.1.i[d] (Authorized Access Control), with the CMMC L1 verbatim text, framework cross-references (FAR 52.204-21(b)(1)(i), NIST 3.1.1), an implementation-narrative editor populated with an Entra ID Conditional Access narrative, status set to Implemented, responsible tool Microsoft Entra ID, and owner / reviewer / last-reviewed fields.](/assets/screenshots/objective-detail.webp)
Objective detail
Verbatim CMMC text in plain view, the framework lineage (FAR / NIST), an implementation-narrative editor, status + responsible tool, owner + reviewer, last-reviewed date and assessment method — every objective gets its own focused workspace.
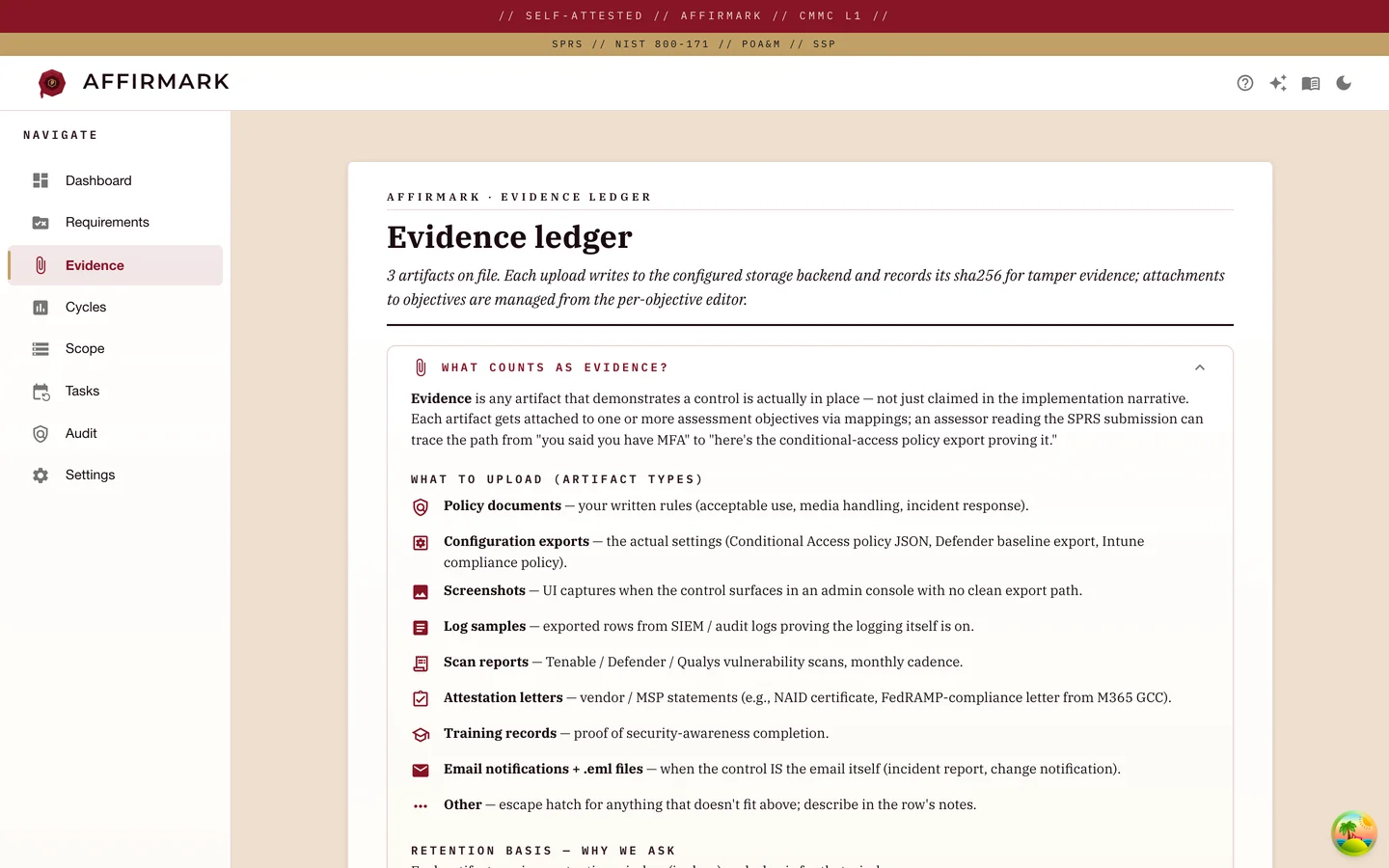
Evidence
Upload form on top — artifact type, source system, retention policy, collection method. Filterable artifact list below, each row hash-stamped for tamper evidence and linked back to the objectives it supports.
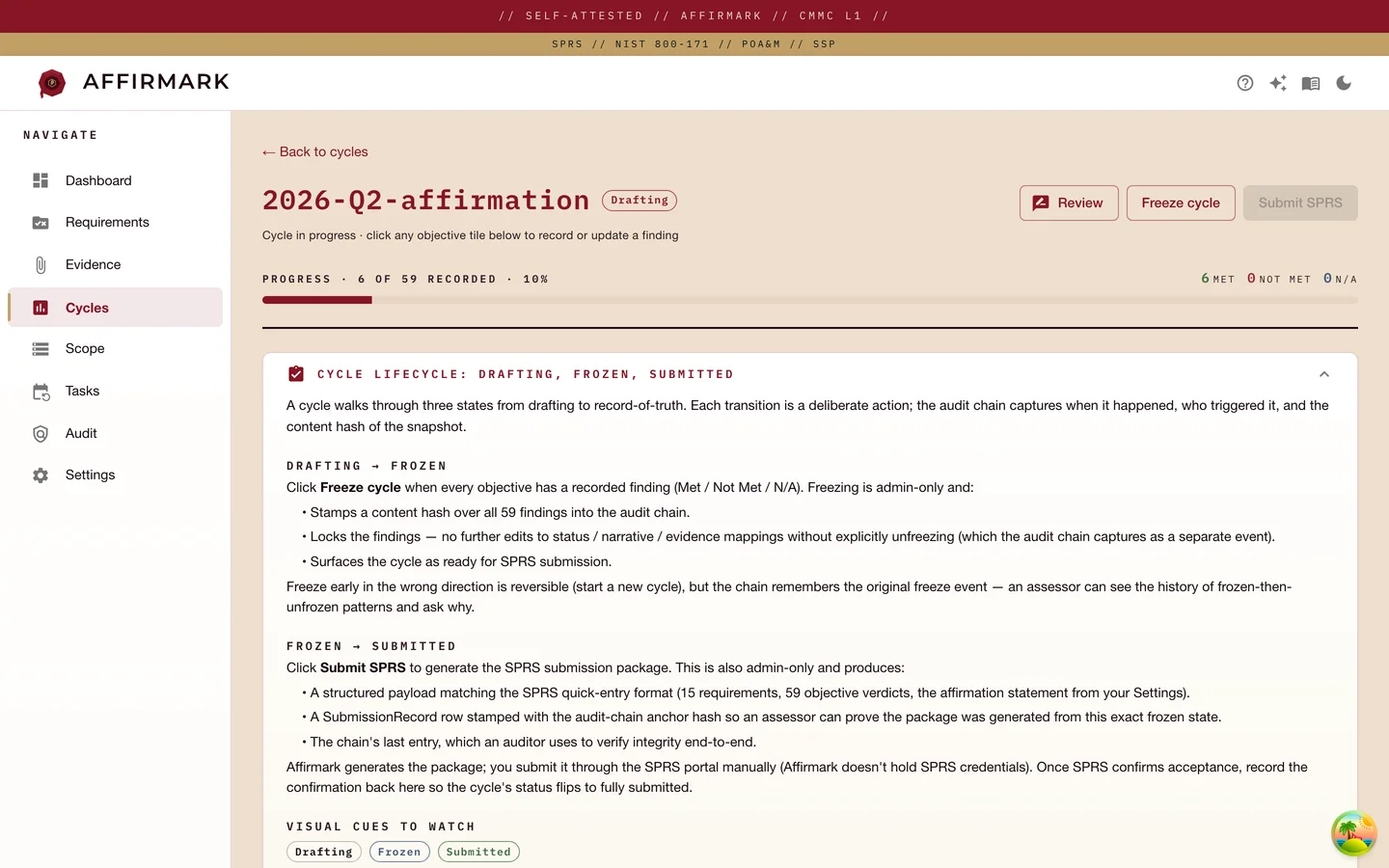
Cycle findings
Examine, interview, or test for every objective. Mark each one met or not applicable. Closing the cycle is blocked while any finding is still open — Affirmark won't let you ship a broken submission.
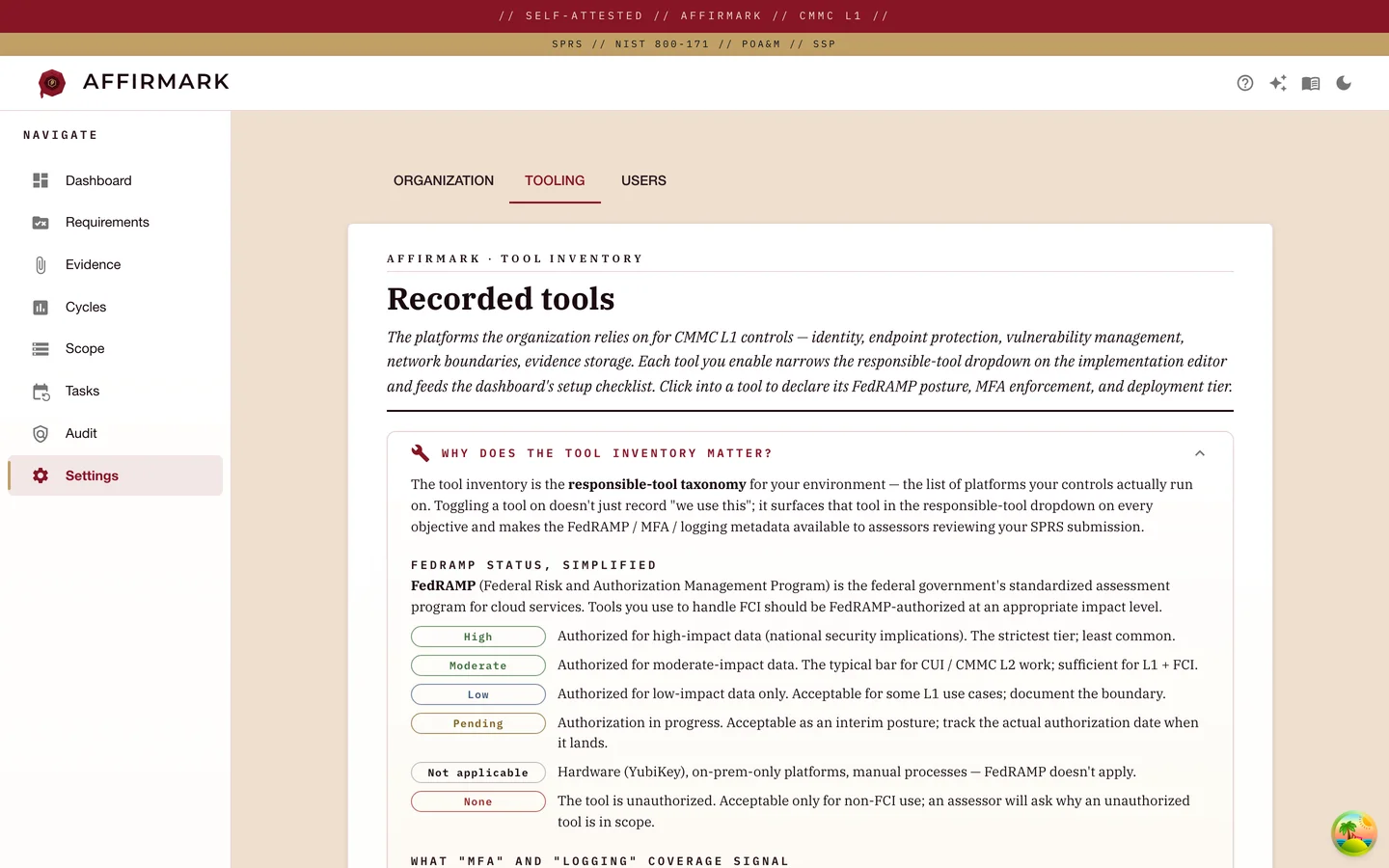
Tooling inventory
Toggle the tools your organization uses; the inventory drives the dashboard checklist and narrows the responsible-tool dropdowns across all 59 objectives. Each enabled tool carries its own FedRAMP status, MFA / logging coverage, and ownership detail page.
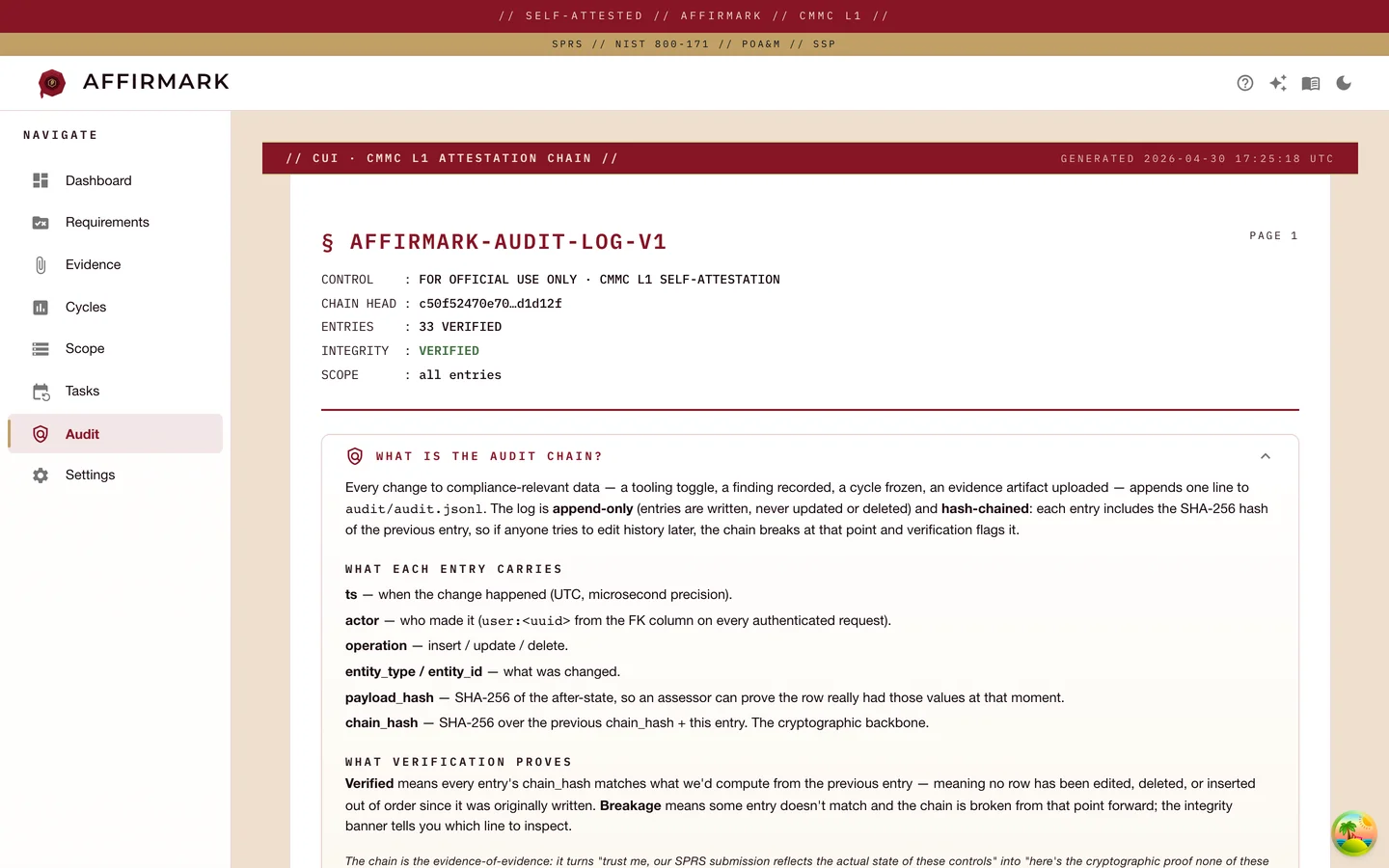
Audit chain
Every mutation is hash-chained: each entry's hash is sha256 of the entry minus the chain field, and includes the previous entry's hash. Tampering breaks the cascade and surfaces in the integrity banner. Filter by actor, entity type, or date range; download the raw JSONL for assessor handoff.
V · Stack
Capture your stack once at setup. Affirmark uses your tooling inventory to narrow responsible-tool dropdowns and pre-populate defaults across all 59 objectives, so every implementation narrative starts at your actual tool, not a blank slate.
Where your users live, where your evidence often lands.
EDR coverage on every workstation in scope.
Configuration and policy enforcement across the fleet.
Retention proof for the data your contracts touch.
Patch posture, scan cadence, exception tracking.
Where your scope assets actually run.
How your users reach in-scope systems.
Don't see your tool? Affirmark accepts any responsible tool you register — these are the names that ship pre-populated in the dropdown.
Posture
Affirmark deploys into your AWS, Azure, GCP, or on-prem environment. The company never holds your CMMC artifacts — your data, your encryption keys, your boundary.
AWS, Azure, GCP, or on-prem — your cloud, your encryption keys, your boundary. Affirmark the company never sees a customer artifact. L2 customers can deploy into AWS GovCloud, Azure Government, or GCP Assured Workloads at IL4/IL5 — government clouds equivalent to FedRAMP Moderate or High, the baseline L2 requires for CUI.
SSO via Microsoft Entra ID, Okta, or Google Workspace. No Affirmark-native passwords to provision or rotate.
Postgres encrypted at rest; evidence files encrypted at rest; TLS on every request. Encryption keys stay in your cloud's key management — AWS KMS, Azure Key Vault, GCP KMS, or your on-prem KMS.
Every write to a compliance entity appends to a hash-chained log. A single command walks the chain end-to-end and exits non-zero on any breakage.
Your data stays in your environment. We provide a shutdown runbook and 30 days of license-transition support if you cancel.
Level 2, when you're ready
Affirmark's data model maps the 15 L1 requirements onto the 110 NIST SP 800-171 R2 controls underneath. When your contracts pull in CUI, the upgrade view shows you which controls you've already proven and which gaps remain. Deploy into AWS GovCloud, Azure Government, or GCP Assured Workloads for the FedRAMP-equivalent posture L2 requires — same evidence, same audit chain, same C3PAO-readable bundle.
FAQ
Click into the ones you care about. If something we should answer is missing, write us at hello@affirmark.com.
You'll have 30+ narratives drafted in week 1 — the 'already implemented' ones (Conditional Access, Defender, BitLocker, drive encryption, MFA) — and a complete first cycle ready for your senior official to sign within 4-8 weeks. Pace depends on how mature your existing controls are, not on Affirmark.
Year 2 is the easier year. Your narratives, evidence, and tooling inventory carry forward; Affirmark surfaces stale evidence (artifacts past their freshness clock) and any objectives where the responsible tool or control state has changed, so you focus on what's actually drifted. Direct ingestion from your IdP, EDR, and scanner inboxes — supported for several Tier-A providers — keeps evidence current between cycles, not just at cycle close. Walk the cycle, refresh the few items that need it, and your senior official re-affirms — typically days, not weeks.
Affirmark connects to your existing tooling and pulls fresh evidence directly: IdP exports, EDR attestation reports, vulnerability scan output, configuration drift snapshots. Two channels — mailbox-driven (Microsoft 365, Google Workspace, Proton) for tools that ship reports by email, and direct API for tools that expose one. Each artifact is hashed, mapped to the relevant objectives, and stamped with a freshness clock the same way an uploaded artifact is. Direct ingestion is supported for several Tier-A providers today, with more wiring in continuously. Manual upload always works as a fallback.
Yes. Affirmark's data model already maps the 15 L1 requirements to NIST SP 800-171 R2 controls — the L2 baseline. When you step up to L2, the upgrade view shows which of the 110 controls you've already implemented and which gaps remain. Same database, same evidence, no re-entry.
Yes. AWS GovCloud, Azure Government (IL4/IL5), and GCP Assured Workloads (IL4/IL5) are all supported deployment targets. L1 customers can deploy to commercial AWS/Azure/GCP; L2 customers handling CUI typically deploy to the government variants for FedRAMP Moderate or High coverage.
Cancel any time. Your data lives in your AWS, Azure, GCP, or on-prem environment, so there's no migration risk — you keep your evidence, narratives, audit chain, and SPRS submission packages forever, even after license expiry. We provide a shutdown runbook plus 30 days of license-transition support if you cancel.
Someone on your team runs a single Terraform module — typically the person who manages your cloud or IT. Clone-to-running is about 30 minutes; deployment support during your first cycle is included. At SMB scale (≤200 users), your AWS / Azure / GCP bill for the Affirmark stack runs roughly $30-80/month — Postgres, object storage, and a small compute footprint.
Affirmark ships releases as versioned Terraform modules and container images. You pin the version; upgrades are explicit. Critical security fixes are flagged in release notes and we email the deployment owner directly when they ship.
Affirmark tracks the L1 Assessment Guide. When DoD revises it, we ship a platform update reflecting the new requirements, objectives, or terminology. Your existing narratives, evidence, and audit chain carry forward — schema versions handle framework rev-bumps without re-entry.
None on your data path. Because Affirmark deploys into your environment, your CMMC artifacts never touch Affirmark's infrastructure. The company runs its own engineering, billing, and CRM on standard SaaS tools, but those never see your data.
Yes — three ways. (1) In-product audit-chain viewer with an integrity banner, per-entry inspector, and filters by actor / entity / date. (2) Raw JSONL export the assessor downloads for offline review. (3) A signed CLI tool we publish — the assessor verifies the chain end-to-end without needing access to your environment.
Yes — for deployment, platform usage, and technical troubleshooting. Email support during US business hours, 72-hour SLA on non-critical issues; 24-hour on critical (deployment broken, audit chain failing, SPRS submission blocked). CMMC interpretation — what counts as adequate for an objective — is out of scope; that's your or your C3PAO's call.
Affirmark gives SMB DoD subcontractors a focused workflow for the 15 L1 requirements and 59 assessment objectives, an assessor-defensible audit chain, and a generated SPRS submission package — without the CMMC-consultant-for-every-step bill. Tell us about your program.